Model Context Protocol (MCP) for Ona Agent
Enable and configure external tools and services for Ona Agent using the Model Context Protocol (MCP).
Ona Agent supports the Model Context Protocol (MCP) to access external tools and resources through MCP servers. Use MCP to extend Ona Agent beyond built-in capabilities with integrations such as GitHub, Linear, or browser automation.
Use your organization’s secret management approach to inject credentials at runtime. Common options:
Guidance:
For blocking system commands executed by Ona Agent itself, see Command deny list.
 Organization owners can control MCP usage across their organization in settings.
To disable MCP:
Organization owners can control MCP usage across their organization in settings.
To disable MCP:
What is MCP?
Model Context Protocol (MCP) is a standardized protocol that enables AI agents to communicate with external services via client/server architecture:- MCP servers provide tools and resources (for example, GitHub MCP server, Linear (MCP directory), Playwright MCP server)
- Ona Agent acts as the MCP client and manages connections
- The AI accesses tools via MCP using JSON-RPC 2.0 over stdio or HTTP
Prerequisites
None! MCP is available out of the box on all tiers.Configure MCP for a project
Create a.ona/mcp-config.json file in your repository to configure MCP servers.
Minimal example
Advanced configuration
Common server configurations
GitHub
Server link: GitHub MCP server (GitHub Docs) Tip: Ensure a Git credential helper is configured sogit credential fill returns a Personal Access Token (for example, run gh auth login).
Linear
Server link: Search for Linear MCP serversPlaywright (browser automation)
Server link: @executeautomation/playwright-mcp-server (npm)Security and controls
Process isolation
- Each MCP server runs as a separate process within your environment. You set per-server environment variables in the MCP config (
env), and if you run the server via Docker you can additionally leverage container isolation - Timeouts can be set per server (
timeout) and globally (globalTimeout) in your MCP config - Defaults: If not set, per-server
timeoutdefaults to 30s and initial connection timeout defaults to 60s - Gitpod environments run in isolated virtual machines for strong workload isolation. See Linux runners overview
Credential management
We recommend using Gitpod Secrets to inject MCP credentials into Ona environments:
- Use Environment Variable secrets for tokens (consume with
\${exec:printenv YOUR_VAR}in MCP config) - Use File secrets when tools expect files (consume with
\${file:/your/mount/path})
- Mounted files provided by your environment or CI/CD (reference with
${file:/path/to/secret}) - Environment variables injected at startup (for non-sensitive config or when files are not feasible)
- On-demand retrieval with
${exec:...}to fetch from an external secret store (for example, AWS Secrets Manager, GCP Secret Manager, Vault)
- Prefer
${exec:...}(fetch at runtime) or mounted files over plain environment variables for sensitive data - Avoid committing secrets to source control; provision them at runtime via your platform of choice
Tool filtering
Organization controls (Enterprise)
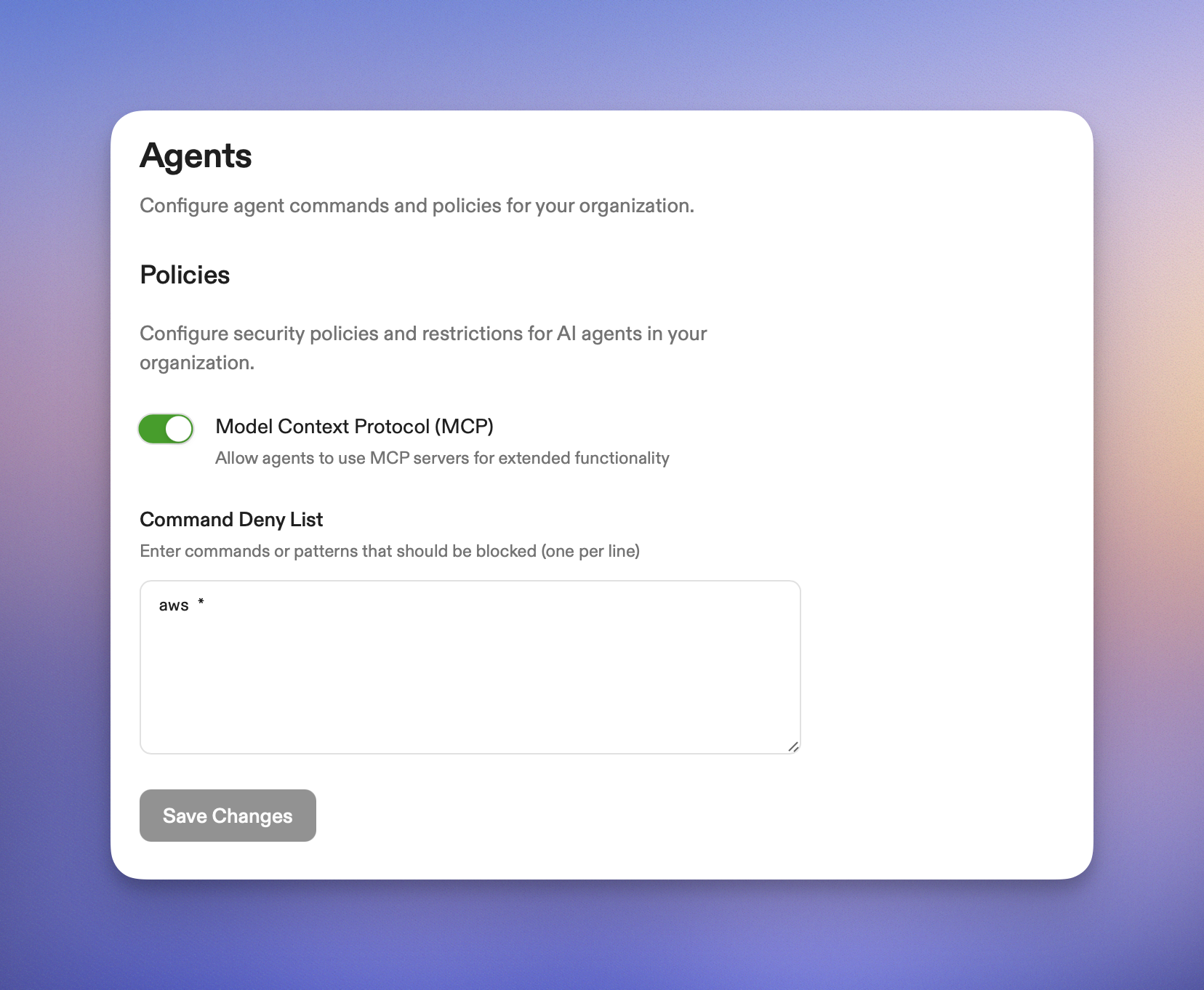
MCP controls in settings for an organization
- Navigate to Settings > Agents
- Locate the MCP controls
- Toggle MCP off to disable Model Context Protocol across all environments in your organization
.ona/mcp-config.jsonfiles in projects are ignored- Ona Agent operates with built-in tools only
- External MCP server connections are blocked
- Changes apply to new Ona Agent sessions; existing sessions should be restarted to apply the policy